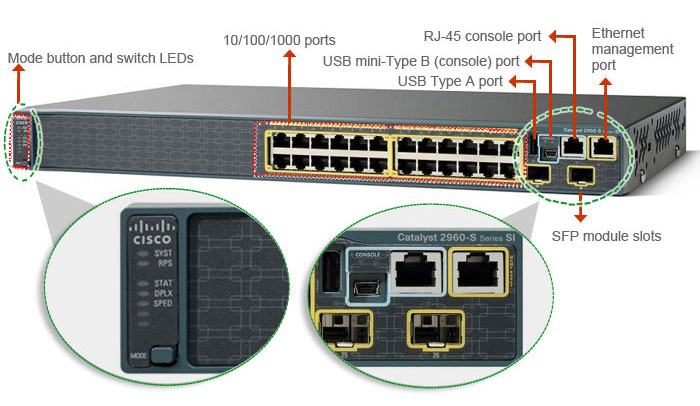
Difference between Console Port and Management Port in Networking Devices
“What’s the difference between the console port and the dedicated management port (fa0), on a Cisco 2960s switch?” Have you ever had this kind of problem? This question was asked by Cisco users, and so many experts shared their suggestions here, let’s learn more about the difference between Console Port and Management Port in networking devices.
- Console port: Requires a dedicated console cable. This means you have to have physical access to the appliance.
- Management Port: Remote access only. You can’t run normal data traffic on this.
The console port is for out of band management & configuration? The dedicated management port is for remote out of band management & configuration?
Console port is NOT an “out of band management” or OoBM because you can’t assign an IP address on it (unless you’ve got a console server). This means you can’t telnet/SSH into a console port. Console port is an “up close and personal” port: You need to have physical access to the appliance in order to use the console port. Management port is an OoBM port.
- Q: I have a Cisco 2960s switch that I did the basic configuration on. The administrative IP address & subnet mask is configured on vlan 1, gi1/0/1. I also have it configured for SSH remote login, and it’s is working. I have to move the management connection to the dedicated management port (fa0). Do I have to put the management port on a vlan to assign an administrative ip address? How do I configure the dedicated management with an IP address, subnet mask & default gateway? I have never done this before.
- I know that the console port is for switch configuration when you have physical access to the switch.
- I know that cannot telnet/SSH into the console port.
- I am using gi1/0/1 on vlan 1 on the Cisco 2960s for my telnet/SSH connection, and I can connect to the switch.
- I need to change the management port that I’m using now(gi1/0/1), to the dedicated management port(fa0) for remote management. Can I use the dedicated management port (fa0) for remote SSH? If I can do that, I’m just not sure what the commands are.
- I guess what I’m asking is, can I use the dedicated management port(fa0) for a remote SSH connection, and how do I do that?
- A: Of course, you can.
- Firstly, for SSH, the IOS used must support crypto.
- Next, configure an IP address on the Fa0 interface. Make sure the IP address is totally different to the management VLAN of your switch.
- Finally, “point” where telnet/ssh goes to: ip tftp interface f0
- Yes, I already have SSH configured with crypto set. When I set the IP for fa0, do I have to assign the interface to a vlan, and do I have to add the gateway as well?
- No you don’t. The IP Address of Fa0 has to be unique. This is the concept of Out of Band Management. It’s like saying you’re entire production network is on the 10.0.0.0/8 subnet but your OoBM network is running on the 192.168.0.0/16 subnet.
- How do I “point” where the telnet/SSH goes to? I don’t understand what you mean by that.
- Use the command “ip tftp interface f0”.
I think I have all the information that I need to try it. I’m going to be doing this configuration on 2960s and I’ve never done this before.
What does the “ip tftp interface f0” command actually do?
That command tells the switch to use fa0 for tftp when you download or upload configs.
However it won’t tell telnet/ssh anything.
If you want to telnet or ssh to the management port from an IP address not in the same subnet as the management port IP the switch needs a default gateway set using the “ip default-gateway <IP address>” command.
I have never used the management port so I can’t say for sure the switch will use this default gateway but it should as long as there are no other L3 interfaces up on the switch.
What do you mean by “L3 interfaces up on the switch”? Do you mean a connection to a router, which is a layer 3 device? No, right now there is nothing connected to the switch except Gi1/0/1 which is the interface that I am using for the management interface through SSH. I am logged in to the switch right now through SSH. I want to change it to the dedicated management interface fa0. Gi1/0/1 is on vlan 1. IP address 192.168.0.149. SM 255.225.254.0. Default gateway, 192.168.1.1. I’m on a /23 network. I think I’m just going to call the Cisco TAC center and have them show me how to do this, because I’m more confused that I was when I first started. I do appreciate you trying to help me.
L3 interface is any port with an IP address assigned to it or a “interface vlan x” with an IP address assigned to it which it sounds like you have.
If you assign an IP to the management port then you can connect to the management port if your PC is on the same IP subnet.
If it isn’t then the 2960 needs to have a default gateway set to know where to send the packets to.
If you already have a default gateway then you may need to change it ie. the default gateway would have to be in the same IP subnet as the IP you assign to the management interface unless you are always going to connect from the same IP subnet as the management interface which I doubt you are.
So the default gateway would be an IP from the same subnet as the IP on the management interface and it would be on a L3 device that routes for the vlans.
If you are currently logged onto the switch and you want to assign an IP from the same IP subnet as is currently on your vlan interface it may not let you do that.
I say may not because like I say I haven’t used the management port and as it does not pass user traffic it may let you do it.
If the switch is in the same building as you it’s worth a try, worst that can happen is you have to go to the switch and log in via the console port to change things.
- Q: I have a question about configuration. Can I configure using management port?
- Usually. For example you might define an explicit IP on the interface or use a DHCP IP.
- Management port don’t use “default-gateway” because there-is-only-one-way-out of the management port.
- How does it know where to send packets for remote subnets i.e. if the destination IP is on the same subnet it sends it direct but if it is on a remote subnet it needs to send packets to a L3 device for routing?
- So it needs some way of knowing which to do.
- Or can you not manage it remotely?
- The Management port, FastEthernet0, doesn’t “understand” default gateway. There is not a lot of stuff you can configure with this port. One of them is an IP address. Think of it as a “PC” and somehow attached to the motherboard using a “psuedo” connection.
- Layer 3 stuff you’re asking. Right, you’re suppose to connect the Management port to a switch. And the switch goes up to another router. The router’s IP address is an OoBM IP address.
So you can’t manage these remotely then and by remotely I mean from a different IP subnet than the IP subnet used for the management port?
Let’s presume that your production network is 10.0.0.0/8. Let’s presume that you’ve got an OoBM network running on 192.168.0.0/16 and this network is NOT routable into the 10.0.0.0/8. The switch will, of course, understand 10.0.0.0/8 network
The router at the core will only talk 192.168.0.0/16. It will not understand 10.0.0.0/8. The OoBM doesn’t really have a link into the 10.0.0.0/8 network. This is what the main intention of the Management port. In some cases I’ve seen, the only way “in” to the OoBM network from the 10.0.0.0/8 network is via a console server.
Because the switch has to know whether the mac address it should use is the mac address of a client ie. the PC is on the same IP subnet or whether the mac should be the L3 devices mac address ?
Never used them so just trying to understand what you can and can’t do this with this port.
Yeah. Me too. And knowing Cisco (lately), documentation (about the configuration guide about the Management port) really s*cks.
I know Management port/interface don’t use default-gateway because I use the port for ZeroTouch Smart Install. All I do is assign (via DHCP) an IP address to the Management port and the VStack Director talks to the client/slave switches just fine. And just because of this, my configuration templates for ZeroTouch SmartInstall always have the Management port disabled and interface has no configuration.
- A console port is special for two reasons. First, it’s “known” to the system as its console port which means the system will send status information to it, and often treat it special when accepting input. Second, the console port is generally wired as a serial port. (It also normally doesn’t have an IP address.)
- The console port was intended for where the system operator controls the system from, usually nearby (physically). (Console ports are/were used for any computer based system.)
- Management ports are generally for remote management using an Ethernet port. On older switches/routers, a device might be configured to use an ordinary Ethernet port for this purpose. On newer switches/routers, a Ethernet port is provided for this purpose. For these, the device may actually use different hardware for port and might treat it internally differently. For example, often the Ethernet management port is only FE, it may not have ASIC support for high speed switching, and it might be in its own predefined VRF. Generally, a management port will have an IP address, but different from IP address spaces used by other hosts.
- Out-of-the-box, a console port will allow you to configure the device, but a management port will often require some additional configuration.
What’s your suggestion? Share it with us…
More summary of the difference between Console Port and Management Port in Networking Devices
Device management is essential in device provisioning, implementation, operations and configuration changes. Inband and out of band (OOB) are 2 management approaches administrators may consider. While OOB management operates on a “management plane” that is separate from the “data plane” used by data traffic on the device, in-band management traffic uses the same data plane as used by data traffic. Hence OOB management can continue to function even during event of data traffic congestion, device glitch or network attacks in addition to improved switch security.
Console Port and dedicated Management port are 2 types of OOB management scenarios. Please note that Console and Management ports support non-transitive traffic and hence can’t be configured.
Below table shares the comparison between Console Port and Management Port
| PARAMETER | CONSOLE PORT | MANAGEMENT PORT |
| IP address Assignment | Can’t give IP address to console Port | IP address can be given to a management port |
| Communication Type | Asynchronous | Synchronous |
| Remote access via Telnet/SSH | No | Yes |
| Access required | Physical access to device required | IP reachability and TCP port 23 (for telnet) or TCP port 443 (for SSH) required or HTTP (80) |
| Segregation type | Physically separate connection | Generally a VRF based traffic segregation |
| Maximum Speed | 0.1 Mbps (115200 bps) | 1 Gbps |
| Connectivity Type | Serial , DB9 , Rj45 | RJ45 |
| Management type | Out of Band Management | Out of Band Management |
| Boot Sequence | Shows Boot sequence | Does not show boot sequence |
| SNMP, Logging on interface | No SNMP, syslog configurable on console interface | SNMP, syslog configurable on management interface |
| Application required | HyperTerminal Telnet/SSH | Web GUI |
| Additional Features | The Console port supports these additional features: • Bit Rate 75, 110, 300, 1200, 2400, 4800, 9600, 19200, 38400, 57600 and 115200 bit/s | The Ethernet management port supports these features: • Express Setup (only in switch stacks) • Network Assistant • Telnet with passwords • TFTP • Secure Shell (SSH) • DHCP-based autoconfiguration • SMNP (only the ENTITY-MIB and the IF-MIB) • IP ping • Speed—10/100/1000 Mbps and autonegotiation • Loopback detection • Cisco Discovery Protocol (CDP) • DHCP relay agent • IPv4 access control lists (ACLs) |
Reference from https://www.ipwithease.com/difference-between-console-port-and-management-port-in-networking-devices/
More Related…
Ethernet Cables, CAT Technical & Physical Differences