The ASA 5505 has 8 ports, but in the base license only 2 vlans can be created. The other 6 ports are simply switch ports that can be placed in the private or outside vlan. If you have an advanced license that allows for DMZs to be created then you can use the physical ports on the back of the ASA as dmzs for things like servers, guest wireless networks, etc.
The ASA 5510 model has mutiple ethernet ports as well, but these are layer3 firewall ports, not bridge/switch ports like in the Cisco ASA 5505.
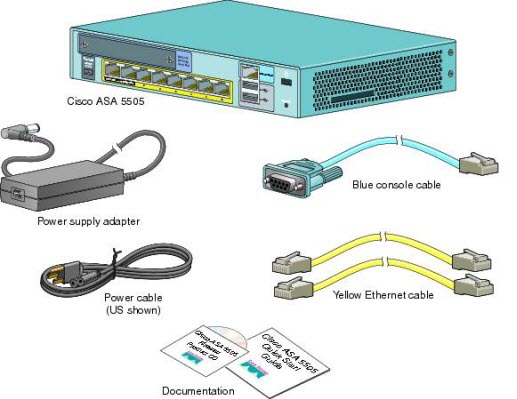
Note: If you purchase Cisco ASA 5505, please verify the package contents.
Cisco ASA 5505 Quick Start Guide: Verifying the Package Contents, Installing the Chassis, Powering on and Verifying Interface Connectivity, Initial Configuration Considerations, Launching ASDM, Running the Startup Wizard, (Optional) Allowing Access to Public Servers Behind the ASA…more detailed info of Cisco asa 5505 start tutorial you can visit: https://www.cisco.com/en/US/docs/security/asa/quick_start/5505/5505-poster.html
The ASA is NOT a router, though and while you can do things on the ASA that can make it act something like a router it is important to understand the differences between true routing and what the ASA actually does.
If you set 2 networks on the Cisco ASA to have the same security zone, you can permit traffic to pass between the interfaces with the same-security-traffic permit inter-interface command.
You can also use nat to nat traffic from one interface to another, and you can create static nats that do not actually nat, but keep state on the connections and pass the traffic w/o changing the addresses or ports.
The Cisco ASA though cannot participate in BGP routing, which makes it impossible to use in most situations where you want to talk to an upstream service provider or use with an MPLS, or GRE tunnel based WAN or value added network. You also cannot use dynamic routing protocols across the ipsec tunnels that the ASA creates, which is the most serious limitation with the ASA in my mind. BSD and/or cisco routers are much better choices for creating ipsec based tunnels across the internet because you can use:
gre + ipsec + BGP
or
gre + ipsec + OSPF/EIGRP (eigrp is cisco proprietary of course)
and get full ip routing with a stateful protocol like BGP across your tunnel. This makes failover between an MPLS cloud and a gre based backup cloud, or 2 gre tunnel paths 1 primary and 1 backup much quicker and simpler to administer than the raw ipsec methods.
The ASA does support OSPF, so it CAN learn about routes from other OSPF speaking gateways. We have found that the OSPF support is buggy in earlier 8.x releases of ASA code on the ASA5505 though. 8.2.2 seems to be pretty solid though. But just because the ASA can speak OSPF does not mean it’s the right choice for routing or connecting between 2 subnets and it’s certainly a poor choice for connecting WAN and internet based private clouds.
Even if you do need to create a security policy between 2 networks (say a research and a production lan) it still may be simpler to use a router with an ACL(s) or a layer 3 switch with ACLs between VLANs than the ASA.
Bottom line: The ASA is a solid firewall but it’s not a router. If you need a router and routing protocols, use a Cisco 1941 (new), Cisco 1841 (used gear). The Cisco 1941s are very comparable to the ASA5510 in terms of throughput. The 1841s are excellent low cost choices for networks that need 30 Mbits/sec or less of IP throughput and 10 to 12 Mbits/sec or less of total IPSEC throughput.
If you want a single box that combines the routing capabilities of a cisco 1941 with the firewalling capabilities of an ASA AND the layer 7 proxy capabilities (dns routing, rinetd tcp port redirect, tcp proxy, web proxy, smtp relay, etc ….) use an OpenBSD router/firewall!
More Cisco ASA Info and Tutorials:
How to Set up a Cisco ASA 5505 Firewall with a Wireless Router?
How to Configure Cisco ASA 5505 Firewall?
How to Connect a Remote Office to Cisco ASA 5510?
How to Configure Dual ISP on Cisco ASA 5505?
Cisco Router with Cisco ASA for Internet Access

Expertise Builds Trust
20+ Years • 200+ Countries • 21500+ Customers/Projects
CCIE · JNCIE · NSE7 · ACDX · HPE Master ASE · Dell Server/AI Expert