Q1: When to apply ACL in or out? I am having a hard time understanding when to apply an ACL on in or out of the interface. When do I want to apply the ACL on the IN, and when do I want to apply the OUT?
In–when you are running traffic coming INTO the interface through an ACL.
Out–when you are running traffic leaving the interface through an ACL.
If you want to filter packets that is coming in, you want to use the in; and if you want to filter packets that is coming out then you use the out.
For example, let’s say you have a topology like this:
PC0——[Router]——Internet
————|
————|
———–PC1
If you want to filter packets coming from the internet, you’re going to use in on the router’s interface facing the internet because the packets from the internet is coming into the router that is why you use in.
If you don’t want PC0 to access the internet, but want it to access PC1, which is in a different subnet, you can use the out on the router’s interface facing the internet. So that every time the PC0 tries to go out to the internet it will be filtered, but if PC0 tries to access PC1, it will be fine.
But see this is where I get a little confused. Wouldn’t I want the ACL for blocking PC0 from the Internet on IN on the router interface for PC0. This way -the ACL would save processing power? Does it matter if the ACL is Standard or Extended?
I think you would require the same or more processing if the out rule were on the PC0 side. Always apply the rule on the interface facing what is being “controlled” if you don’t want PC1 to communicate with PC0 then the out rule would be on the PC0 side.
If the data is moving from the internet to PC0, it is flowing (in the example picture) from right to left. When it hits the router, it’s flowing IN the right-most port on the router, and back OUT the left port.
Similarly when data is flowing from PC0 out to the internet, it’s flowing from left to right; IN the left-most port of the router and OUT the right-most port. Regarding where you would want to place an ACL; that depends on if it’s a standard or extended ACL. I don’t know if you’re studied that material yet, but once you do it makes more sense about WHERE you would want to apply it.
Q2: Access List In/Out clarification. I have a clarifying question re: placing an access list into or out of an interface.
Let’s say for the sake of keeping it basic that I have this topology:
PC1—>E0Router1E1<—-PC2
If I want to apply an access list that deny’s all packets with source add pc1 to PC2 can I do it two ways:
Place an IN access-group command on E0 or an OUT access-group command on E1?
Would the Cisco recommended way be to put it on E1 since it’s the closest to the destination?
This is regarding Standard ACL’s but I’m assuming this will also come up on Extended ones.
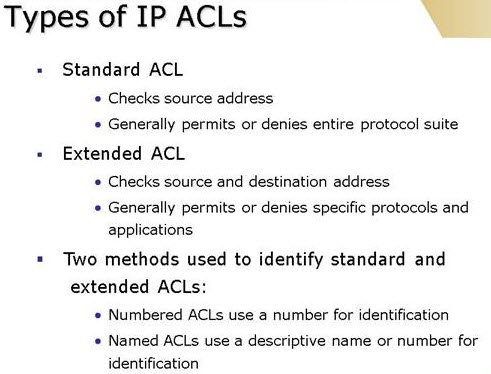
- Standard ACLs should be placed as close to the destination as possible so they do not block traffic you do not wish to block.
- Extended ACLs should be placed as close to the source as possible.
There’s just two different ways of saying the same thing but there is a best practice (placing close to destination in standard and close to source in extended.) I thought there was some secret algorithm you had to run to determine which one it was.
As said above, for _extended_ ACL’s you always want them as close to the source as possible. The reason this is done is to have the traffic dropped *before* the CPU has to spend cycles looking at the packet and making judgments of where to send it. …
Q3: Cisco ACL in/out question. When working with Cisco ACLs, the access-groups are applied to individual interfaces.
int s0
access – group 101 in
access – group 102 out
My understanding is that “in” is always traffic going towards the router, and “out” is always traffic going away from the router. Like this:
in = leaving the out = leaving the company
private network going to the Internet
—————-> ———————–>
———-
e0 | router | s0
———-
out = entering the in = coming into the
private network company from the Internet
<————– <———————-
So packets from the internal network to the Internet are “in” on e0 and “out” on s0.
Are my assumptions of in/out correct?
Also, can you split the in/out between interfaces like this:
int s0
access-group 101 in
int e0
access-group 102 in
Or should they be applied to the same interface?
Since it’s applied to the interface, you must consider it that way, not ‘to the router’ per say…
So, from the interface perspective:
int s0
access-group 101 in
access-group 102 out
Anything leaving interface s0 will be covered by 102, anything entering the interface s0 will be covered by 101. Where you put the ACL is really up to you. I’ve seen it done both ways (sorry, had to edit this part, must remember to have a cup of coffee before reading/responding to posts), generally with the consideration of avoiding passing packets through the router only to drop them as they attempt to leave the interface…
Indeed, you usually try to drop traffic as close to the edge as possible.
However, one reason for filtering out on an interface could be if you have a router with multiple interfaces and wanted to secure (default deny) the zone behind one of those interfaces from all other interfaces. Then it’s much easier to “deny ip any any” out on said interface than try to deny in based on destination on all other interfaces…
Standard ACL should be placed close to destination Extended ACL should be placed close to source that should be your guide when you think about placing ACLs, the other is really up to your wishes. Oh, and you shouldn’t watch it from the routers perspective, take the interfaces point of view when you say in it means inbound traffic on that interface out means outbound traffic on that interface so on every interface you can have in and out…
More Related Cisco and Networking Reviews: https://blog.router-switch.com/category/networking-2/ and https://blog.router-switch.com/category/hardware/

Expertise Builds Trust
20+ Years • 200+ Countries • 21500+ Customers/Projects
CCIE · JNCIE · NSE7 · ACDX · HPE Master ASE · Dell Server/AI Expert