Introduction
In the rapidly evolving digital world, the role of Chief Information Security Officers (CISOs) is more critical than ever. The tools and strategies that once safeguarded organizations are no longer sufficient in the face of emerging threats and evolving technologies. This article explores the key insights from the 2023 CISO Survival Guide, co-authored by Cisco Investments in collaboration with cybersecurity-focused venture capitalists within the startup landscape, including Forgepoint Capital, NightDragon, and Team8. These insights shed light on the changing cybersecurity landscape and how CISOs can adapt to protect their organizations effectively.
Challenges in the Cybersecurity Landscape
CISOs are at the forefront of ensuring the security of sensitive enterprise applications and the management of dynamic user access. However, they face numerous challenges in the current landscape, including:
Enterprise Collaboration Tools: The proliferation of collaboration tools has created new security vulnerabilities that need to be addressed.
Remote and Hybrid Workforces: Remote and hybrid work arrangements have expanded the attack surface, making it more challenging to secure enterprise networks.
Extended Supply Chains: Lengthening supply chains introduce additional points of vulnerability that require protection.
Unification: A Common Theme
One common theme that resonates across the insights from various experts is the need for unification in cybersecurity. This unification includes:
Interoperability: The demand for more interoperability and less friction between security solutions.
Decipherable Data: The importance of having decipherable data when making crucial security decisions.
Key Priorities
The 2023 CISO Survival Guide highlights several key priorities for CISOs:
Identity and Access Management (IAM): 85% of IT decision-makers prioritize IAM investments. However, the lack of a unified platform across IAM, Identity Governance and Administration (IGA), and Privileged Access Management (PAM) remains a critical pain point.
Cloud Security: Cloud Security is a top priority, with a focus on bridging the gap between prevention and post-breach security. The emergence of Cloud Native Application Protection Platform is set to address this challenge comprehensively.
Data Security: Controlling access to information, especially data identity and privileged access management, is essential. Data security encompasses aspects like Data Access Control and Data Loss Prevention.
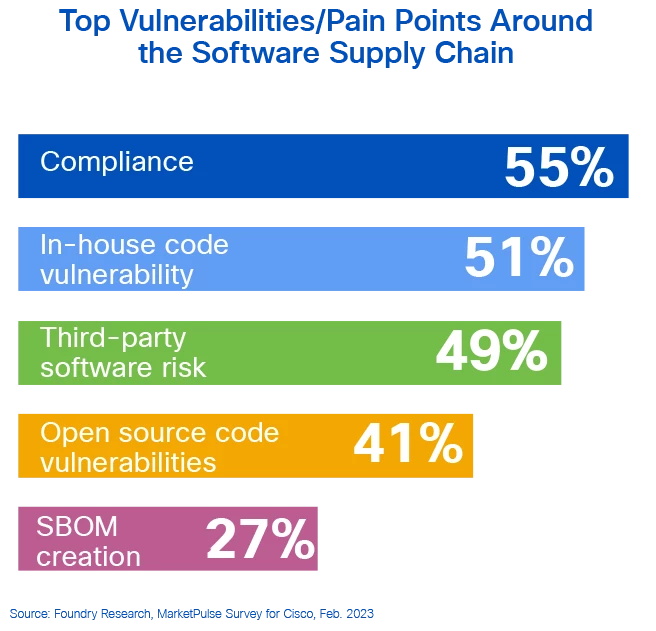
Software Supply Chain: The software supply chain is a vulnerable point, and agile DevOps practices have accelerated development lifecycles. Visibility and governance in the software supply chain are essential to address security concerns effectively.
The Path Forward
The cybersecurity industry is undergoing dynamic changes, including the rise of concepts like SASE (Secure Access Service Edge), Zero Trust, CNAPP (Cloud Native Application Protection Platform), DSPM (Data Security and Privacy Management), SSPM (Software Supply Chain Protection Management), and DRPS (Digital Risk Protection Solutions). To navigate this landscape effectively, a focus on core use cases and differentiation on functional axes is becoming increasingly critical.
Conclusion
The 2023 CISO Survival Guide provides valuable insights into the evolving cybersecurity landscape. By addressing the challenges, priorities, and the need for unification, CISOs can better prepare their organizations to face the cybersecurity challenges of today and tomorrow. To explore the full depth of insights from the guide and discover how startup trends will impact cybersecurity in the year ahead, visit Router-switch.com.
Read More:
Igniting the Future of ICT: An Invitation to Router-switch.com’s InnovateTech Speaker Program
Using Huawei SFP-10G-LR Optical Transceivers to Strengthen Your Network