Knowing how to properly use logging is a necessary skill for any network administrator, and the Cisco IOS offers many options for logging.
Logging can use for fault notification, network forensics, and security auditing.
Cisco routers log messages can handle in five different ways:
Console logging: By default, the router sends all log messages to its console port. Hence only the users that are physically connected to the router console port can view these messages.
Terminal logging: It is similar to console logging, but it displays log messages to the router’s VTY lines instead. This is not enabled by default
Buffered logging: This type of logging uses router’s RAM for storing log messages. buffer has a fixed size to ensure that the log will not deplete valuable system memory. The router accomplishes this by deleting old messages from the buffer as new messages are added.
Syslog Server logging: The router can use syslog to forward log messages to external syslog servers for storage. This type of logging is not enabled by default.
SNMP trap logging: The router is able to use SNMP traps to send log messages to an external SNMP server.
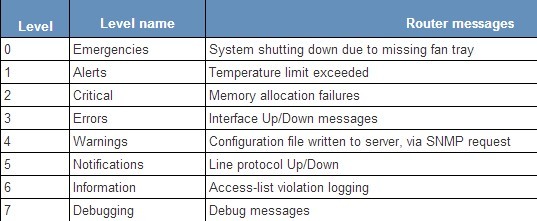
Sample router log messages, eight different logging levels.
Level |
Level name |
Router messages |
| 0 | Emergencies | System shutting down due to missing fan tray |
| 1 | Alerts | Temperature limit exceeded |
| 2 | Critical | Memory allocation failures |
| 3 | Errors | Interface Up/Down messages |
| 4 | Warnings | Configuration file written to server, via SNMP request |
| 5 | Notifications | Line protocol Up/Down |
| 6 | Information | Access-list violation logging |
| 7 | Debugging | Debug messages |
Configuration Overview:
1. Console logging:
The router does not check if a user is logged into the console port or a device is attached to it; if console logging is enabled, messages are always sent to the console port that can cause CPU load.
To stop the console logging, use the “no logging console” global configuration command .you might want to limit the amount of messages sent to the console with the “logging console level” configuration command (for example, logging console Informational).
2. Buffered logging:
You want your router to record log messages, instead of just displaying them on the console.To use logging buffered configuration command to enable the local storage of router log messages:
Router#configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#logging buffered informational
Router(config)#end
You can also Set the Log Size on router.
Router#configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#logging buffered 64000
Router(config)#end
3. Terminal logging
You want the router to display log messages to your VTY session in real time.Use the terminal monitor command to enable the displaying of log messages to your VTY:
Router#terminal monitor
Router#
To disable logging to your VTY session, use the following command:
Router#terminal no monitor
Router#
4. Syslog Server logging:
You want to send log messages to a remote syslog server. By using this we can send messages to an external device for storing this logs and the storage size does depend on the available disk space of the external syslog server. This option is not enabled by default.
If you have any syslog server please find the below simple config.
router#conf t
Router(config#logging host x.x.x.x
Router(config)#logging traps (i.e 0 1 2 3 4 5 .. according to your requirement)
before enabling logging be sure that your router is properly configure to collect proper time from any NTP server or manually configure to get time
Command to set time manually on router is (set clock) or to use ntp server use “ntp server x.x.x.x” to sync clock to router.
Use the logging source-interface configuration command to specify a particular IP address for syslog messages:
Router(config)#logging source-interface Loopback0
5. Clearing the Router’s Log
Use the clear logging command to clear the router’s internal log buffer:
Router#clear logging
Clear logging buffer [confirm]<enter>
Router#
6. To display the state of system logging (syslog) and the contents of the standard system logging message buffer, use the show logging privileged EXEC command.
Router# show logging
Syslog logging: enabledConsole logging: disabled
Monitor logging: level debugging, 266 messages logged.
Trap logging: level informational, 266 messages logged.
Logging to 10.1.1.1
SNMP logging: disabled, retransmission after 30 seconds
0 messages logged
Router#.
Common logging errors
Logging can be frustrating at times. Here we listed three common errors as follows.
Not setting the terminal to monitor logging
If you Telnet into a router and can’t see some of the logging you’re expecting, check to see if you’ve set your terminal to monitor the logging. You can enable this with the terminal monitorcommand. To disable it, use the terminal no monitor command.
To determine whether you’ve enabled monitoring, use the show terminal command, and look for the following:
Capabilities: Receives Logging Output
If you see this, you’re monitoring logging output. If it returns none for capabilities, then the monitoring is off.
Using the incorrect logging level
If you can’t see logging output, you should also check whether you’ve set the level correctly. For example, if you’ve set the console logging to emergencies but you’re running debugging, you won’t see any debugging output on the console.
To determine the set level, use the show logging command. Keep in mind that you need to set the level to a higher number to see all levels below it. For example, setting logging at debugging shows you every other level.
In addition, make sure you match the type of logging that you want to see with the level you’re configuring. If you configure monitor logging to debug but you’re on the console and you’ve set it to informational, you won’t see the debug output on the console.
Displaying the incorrect time and date in logs
You may see log messages that don’t exhibit the correct date and time. There are a variety of options to control the date and time that appear on logging output (either to the screen or to the buffer). To control this, use the following command:
Router(config)# service timestamps debug ?
datetime Timestamp with date and time
uptime Timestamp with system uptime
Note: Remember that many problems require some kind of historical log to help find a solution. That’s why it’s important to make sure you’ve properly configured logging so you can use your logs to see the past.
Doc Reference from https://supportforums.cisco.com/docs/DOC-4788 & techrepublic.com
More Cisco IOS Tips:
Cisco IOS Updates Fix Eight Denial of Service Vulnerabilities
Static Route Configuration between Cisco IOS and IOS XR Comparison
Top 10 Commands Every Cisco IOS User Should Know

Expertise Builds Trust
20+ Years • 200+ Countries • 21500+ Customers/Projects
CCIE · JNCIE · NSE7 · ACDX · HPE Master ASE · Dell Server/AI Expert