What is vlan and how are vlans divided? In this issue, let’s take a look at the six ways of VLAN division:
What is vlan and how are vlans divided? In this issue, let’s take a look at the six ways of VLAN division:
1. Basic knowledge of VLAN
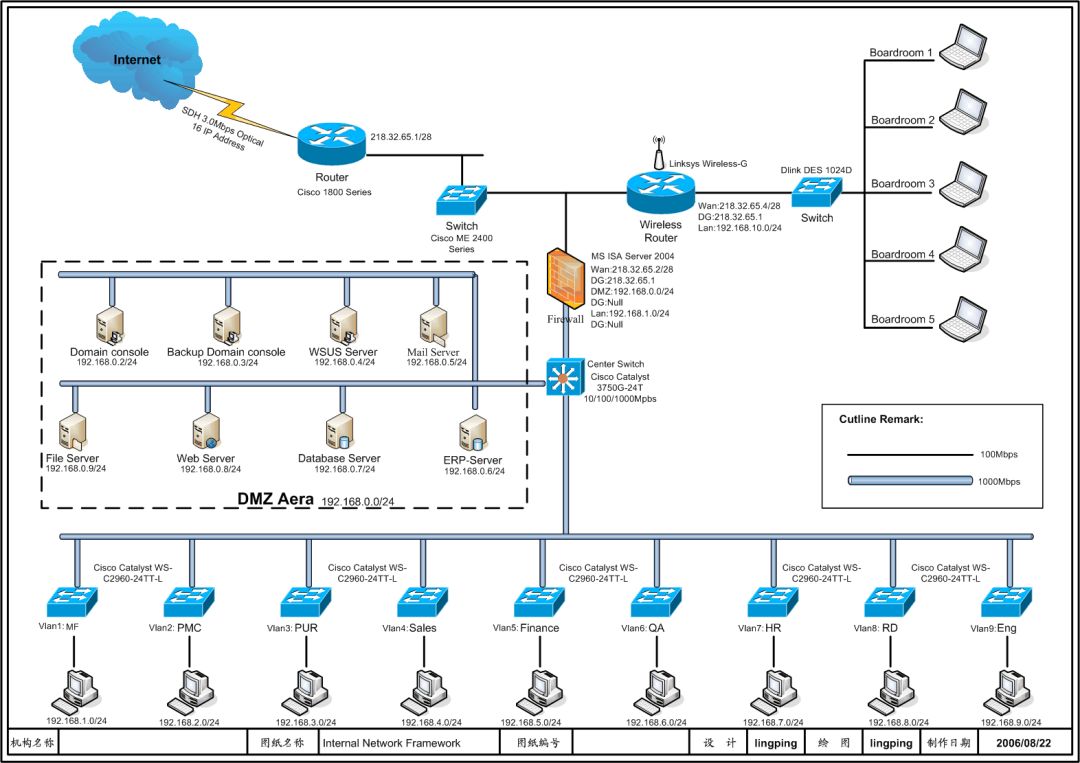
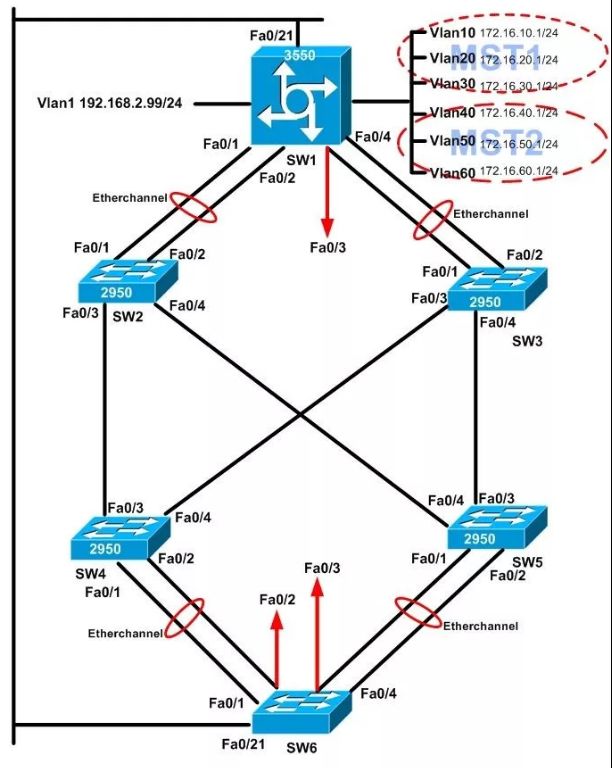
The Chinese name of VLAN is “Virtual Local Area Network”, not “VPN” (Virtual Private Network). VLAN is a new data exchange technology that logically divides LAN devices (note, not physically) into network segments to realize virtual workgroups. This emerging technology is mainly used in switches and routers, but the mainstream application is still in switches. But not all switches have this function, only switches above the third layer of the VLAN protocol have this function, you can check the manual of the corresponding switch to know.
In a shared network, a physical network segment is a broadcast domain. In a switched network, a broadcast domain can be a virtual network segment composed of a group of arbitrarily selected second-layer network addresses (MAC addresses). In this way, the division of workgroups in the network can break through the geographic location restrictions in the shared network, and be divided entirely according to management functions. This workflow-based grouping mode greatly improves the management function of network planning and reorganization.
Workstations in the same VLAN, regardless of which switch they are actually connected to, communicate between them as if they were on separate switches. The broadcast in the same VLAN can only be heard by the members of the VLAN, and will not be transmitted to other VLANs, so that the generation of unnecessary broadcast storms can be well controlled. At the same time, if there is no routing, different VLANs cannot communicate with each other, which increases the security between different departments in the enterprise network.
2, VLAN division method
The implementation methods of VLAN on the switch can be roughly divided into six categories:
1.VLAN based on port division:
The most common and efficient method, according to the division of Ethernet switch ports, each group forms a virtual network, which is convenient for defining members. When mutual visits are required, routers and MAC address filtering can be used to prevent internal theft of IP addresses. Applicable to various large and small networks, but the user needs to redefine the port when changing the port. Enterprises segment virtual networks for enhanced management, security and control over data broadcasting.
2.VLAN division based on MAC address:
According to the unique MAC address of the host, the implementation method is to track the MAC address of each network card. When users move, VLANs do not need to be reconfigured because they are based on users rather than switch ports. The advantage lies in adapting to user mobility, but user-by-user configuration is required during initialization, which is suitable for small LANs. However, the configuration is cumbersome and may reduce switch efficiency since there may be multiple VLAN group members per port. For users who change laptops frequently, VLANs need to be configured frequently.
3.VLAN division based on network layer protocol:
VLANs are divided according to protocols such as IP, IPX, DECnet, and AppleTalk, allowing broadcast domains to span multiple VLAN switches, facilitating the organization of users for applications and services. Users can move freely and keep VLAN identity.
The advantage is that there is no need to reconfigure the VLAN attribution after the user moves, and the division of VLANs according to the protocol is beneficial to network management, and there is no need to attach frame tags to reduce traffic. The disadvantage is that the efficiency is low, and checking the network layer address is time-consuming, compared with the first two methods. It requires higher technology for the chip to support IP frame header inspection, and different manufacturers have different implementations.
4.IP multicast as VLAN division:
Treat each IP multicast group as a VLAN, which is suitable for cross-wide area networks, flexible and easy to expand, but not suitable for local area networks because of limited efficiency.
5.Policy division VLAN:
Based on the policy including port, MAC, IP, protocol, etc., the appropriate division type can be selected according to the management mode and requirements.
6.User-defined, non-authorized VLAN division:
Define and design VLAN according to the special requirements of users, allowing non-VLAN users to access, but authentication is required to join.
 Advantages of VLANs:
Advantages of VLANs:
Increase network security: Each VLAN is an independent broadcast domain, and isolation improves network security. Confidential data can be transmitted in secure VLANs with access control, and switch ports can be grouped based on application type and access privileges.
Transform your network with VLAN technology. Visit Router Switch for a wide range of Cisco products, including cutting-edge VLAN solutions. Upgrade now for efficient, secure, and optimized networks. Elevate your integration game with Router Switch today.
Check More Router Switch Products:
Read More:
Igniting the Future of ICT: An Invitation to Router-switch.com’s InnovateTech Speaker Program